Cybersecurity researchers have shed light on a Chinese-speaking cybercrime group codenamed UAT-8099 that has been attributed to search engine optimization (SEO) fraud and theft of high-value credentials, configuration files, and certificate data.
The attacks are designed to target Microsoft Internet Information Services (IIS) servers, with most of the infections reported in India, Thailand, Vietnam, Canada, and Brazil, spanning universities, tech firms, and telecom providers. The group was first discovered in April 2025. The targets are primarily mobile users, encompassing both Android and Apple iPhone devices.
UAT-8099 is the latest China-linked actor to engage in SEO fraud for financial gain. As recently as last month, ESET revealed details of another threat actor named GhostRedirector that has managed to compromise at least 65 Windows servers primarily located in Brazil, Thailand, and Vietnam with a malicious IIS module codenamed Gamshen to facilitate SEO fraud.
“UAT-8099 manipulates search rankings by focusing on reputable, high-value IIS servers in targeted regions,” Cisco Talos researcher Joey Chen said. “The group maintains persistence and alters SEO rankings using web shells, open-source hacking tools, Cobalt Strike, and various BadIIS malware; their automation scripts are customized to evade defenses and hide activity.”
Once a vulnerable IIS server is found – either via security vulnerability or weak settings in the web server’s file upload feature – the threat actor uses the foothold to upload web shells to conduct reconnaissance and gather basic system information. The financially motivated hacking group subsequently enables the guest account to escalate their privileges, all the way to the administrator, and use it to enable Remote Desktop Protocol (RDP).
UAT-8099 has also been observed taking steps to plug the initial access pathway to maintain sole control of the compromised hosts and prevent other threat actors from compromising the same servers. In addition, Cobalt Strike is deployed as the preferred backdoor for post-exploitation.
In order to achieve persistence, RDP is combined with VPN tools like SoftEther VPN, EasyTier, and Fast Reverse Proxy (FRP). The attack chain culminates with the installation of BadIIS malware, which has been put to use by multiple Chinese-speaking threat clusters like DragonRank and Operation Rewrite (aka CL-UNK-1037).
UAT-8099 uses RDP to access IIS servers and search for valuable data within the compromised host using a graphical user interface (GUI) tool named Everything, which is then packaged for either resale or further exploitation. It’s not currently clear how many servers the group has compromised.
The BadIIS malware deployed in this case, however, is a variant that has tweaked its code structure and functional workflow to sidestep detection by antivirus software. It functions similarly to Gamshen in that the SEO manipulation component kicks in only when the request originates from Google (i.e., User-Agent is Googlebot).
BadIIS can operate in three different modes –
- Proxy, which extracts the encoded, embedded command-and-control (C2) server address and uses it as a proxy to retrieve content from a secondary C2 server
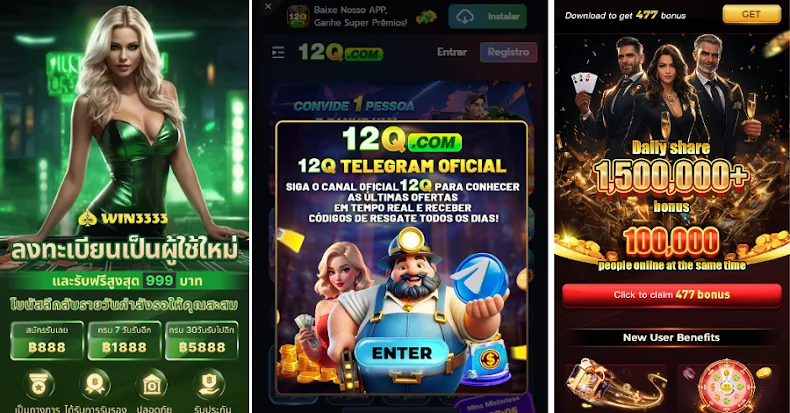
- Injector, which intercepts browser requests originating from Google search results, connects to the C2 server to retrieve JavaScript code, embeds the downloaded JavaScript into the HTML content of the response, and returns the altered response back to redirect the victim to the chosen destination (unauthorized advertisements or illegal gambling websites)
- SEO fraud, which compromises multiple IIS servers to conduct SEO fraud by serving backlinks to artificially boost website rankings
“The actor employs a conventional SEO technique known as backlinking to boost website visibility,” Talos said. “Google’s search engine uses backlinks to discover additional sites and assess keyword relevance.”
“A higher number of backlinks increases the likelihood of Google crawlers visiting a site, which can accelerate ranking improvements and enhance exposure for the webpages. However, simply accumulating backlinks without regard to quality can lead to penalties from Google.”