Cybersecurity researchers have flagged a new malicious extension in the Open VSX registry that harbors a remote access trojan called SleepyDuck.
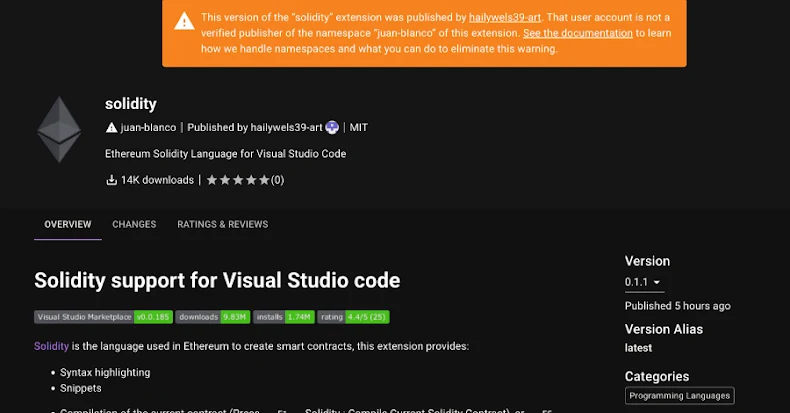
According to Secure Annex’s John Tuckner, the extension in question, juan-bianco.solidity-vlang (version 0.0.7), was first published on October 31, 2025, as a completely benign library that was subsequently updated to version 0.0.8 on November 1 to include new malicious capabilities after reaching 14,000 downloads.
“The malware includes sandbox evasion techniques and utilizes an Ethereum contract to update its command and control address in case the original address is taken down,” Tuckner added.
Campaigns distributing rogue extensions targeting Solidity developers have been repeatedly detected across both the Visual Studio Extension Marketplace and Open VSX. In July 2025, Kaspersky disclosed that a Russian developer lost $500,000 in cryptocurrency assets after installing one such extension through Cursor.
In the latest instance detected by the enterprise extension security firm, the malware is triggered when a new code editor window is opened or a .sol file is selected.
Specifically, it’s configured to find the fastest Ethereum Remote Procedure Call (RPC) provider to connect to in order to obtain access to the blockchain, initialize contact with a remote server at “sleepyduck[.]xyz” (hence the name) via the contract address “0xDAfb81732db454DA238e9cFC9A9Fe5fb8e34c465,” and kicks off a polling loop that checks for new commands to be executed on the host every 30 seconds.
It’s also capable of gathering system information, such as hostname, username, MAC address, and timezone, and exfiltrating the details to the server. In the event the domain is seized or taken down, the malware has built-in fallback controls to reach out to a predefined list of Ethereum RPC addresses to extract the contract information that can hold the server details.
What’s more, the extension is equipped to reach a new configuration from the contract address to set a new server, as well as execute an emergency command to all endpoints in the event that something unexpected occurs. The contract was created on October 31, 2025, with the threat actor updating the server details from “localhost:8080” to “sleepyduck[.]xyz” over the course of four transactions.
It’s not clear if the download counts were artificially inflated by the threat actors to boost the relevance of the extension in search results – a tactic often adopted to increase the popularity so as to trick unsuspecting developers into installing a malicious library.
“The download counts likely are manipulated making it hard to know exactly,” Tuckner told The Hacker News. “This is very likely done to make it more relevant in the search results for Cursor/Open VSX.”
The development comes as the company also disclosed details of another set of five extensions, this time published to the VS Code Extension Marketplace by a user named “developmentinc,” including a Pokémon-themed library that downloads a batch script miner from an external server (“mock1[.]su:443”) as soon as it’s installed or enabled, and executes it using “cmd.exe.”
The script file, besides relaunching itself with administrator privileges using PowerShell and configuring Microsoft Defender Antivirus exclusions by adding every drive letter from C: through Z:, downloads a Monero mining executable from “mock1[.]su” and runs it.
The extensions uploaded by the threat actor, now no longer available for download, are listed below –
- developmentinc.cfx-lua-vs
- developmentinc.pokemon
- developmentinc.torizon-vs
- developmentinc.minecraftsnippets
- developmentinc.kombai-vs
Users are advised to exercise caution when it comes to downloading extensions, and make sure that they are from trusted publishers. Microsoft, for its part, announced back in June that it’s instituting periodic marketplace-wide scans to protect users against malware. Every removed extension from the official marketplace can be viewed from the RemovedPackages page on GitHub.