Cybersecurity researchers have shed light on the inner workings of a botnet malware called PolarEdge.
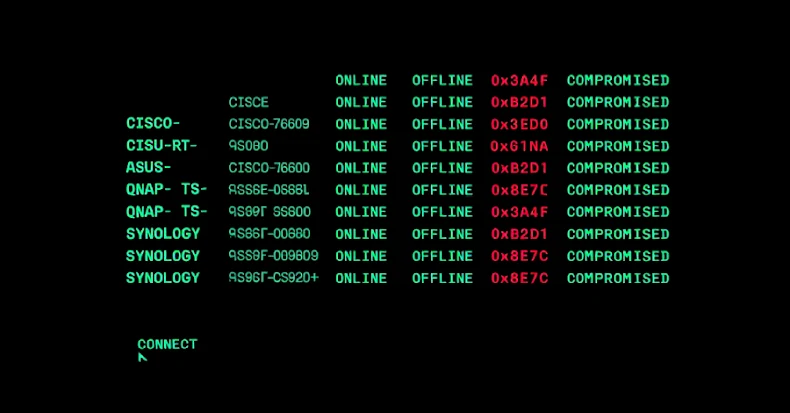
PolarEdge was first documented by Sekoia in February 2025, attributing it to a campaign targeting routers from Cisco, ASUS, QNAP, and Synology with the goal of corralling them into a network for an as-yet-undetermined purpose.
The TLS-based ELF implant, at its core, is designed to monitor incoming client connections and execute commands within them.
Then, in August 2025, attack surface management platform Censys detailed the infrastructural backbone powering the botnet, with the company noting that PolarEdge exhibits characteristics that are consistent with an Operational Relay Box (ORB) network. There is evidence to suggest that the activity involving the malware may have started as far back as June 2023.
In the attack chains observed in February 2025, the threat actors have been observed exploiting a known security flaw impacting Cisco routers (CVE-2023-20118) to download a shell script named “q” over FTP, which is then responsible for retrieving and executing the PolarEdge backdoor on the compromised system.
“The backdoor’s primary function is to send a host fingerprint to its command-and-control server and then listen for commands over a built-in TLS server implemented with mbedTLS,” the French cybersecurity company said in a technical breakdown of the malware.
PolarEdge is designed to support two modes of operation: a connect-back mode, where the backdoor acts as a TLS client to download a file from a remote server, and debug mode, where the backdoor enters into an interactive mode to modify its configuration (i.e., server information) on-the-fly.
The configuration is embedded in the final 512 bytes of the ELF image, obfuscated by a one-byte XOR that can be decrypted with single-byte key 0x11.
However, its default mode is to function as a TLS server in order to send a host fingerprint to the command-and-control (C2) server and wait for commands to be sent. The TLS server is implemented with mbedTLS v2.8.0 and relies on a custom binary protocol for parsing incoming requests matching specific criteria, including a parameter named “HasCommand.”
 |
| Encryption algorithms used to obfuscate parts of the backdoor |
If the “HasCommand” parameter equals the ASCII character 1, the backdoor proceeds to extract and run the command specified in the “Command” field and transmits back the raw output of the executed command.
Once launched, PolarEdge also moves (e.g., /usr/bin/wget, /sbin/curl) and deletes certain files (“/share/CACHEDEV1_DATA/.qpkg/CMS-WS/cgi-bin/library.cgi.bak”) on the infected device, although the exact purpose behind this step is unclear.
Furthermore, the backdoor incorporates a wide range of anti-analysis techniques to obfuscate information related to the TLS server setup and fingerprinting logic. To evade detection, it employs process masquerading during its initialization phase by choosing from a predefined list a name at random. Some of the names included are: igmpproxy, wscd, /sbin/dhcpd, httpd, upnpd, and iapp.
“Although the backdoor does not ensure persistence across reboots, it calls fork to spawn a child process that, every 30 seconds, checks whether /proc/
The disclosure comes as Synthient highlighted GhostSocks’ ability to convert compromised devices into SOCKS5 residential proxies. GhostSocks is said to have been first advertised under the malware-as-a-service (MaaS) model on the XSS forum in October 2023.
It’s worth noting that the offering has been integrated into Lumma Stealer as of early 2024, allowing customers of the stealer malware to monetize the compromised devices post-infection.
“GhostSocks provides clients with the ability to build a 32-bit DLL or executable,” Synthient said in a recent analysis. “GhostSocks will attempt to locate a configuration file in %TEMP%. In the scenario that the configuration file cannot be found, it will fall back to a hard-coded config.”
The configuration contains details of the C2 server to which a connection is established for provisioning the SOCKS5 proxy and ultimately spawning a connection using the open-source go-socks5 and yamux libraries.