Artificial intelligence (AI) company Anthropic has begun to roll out a new security feature for Claude Code that can scan a user’s software codebase for vulnerabilities and suggest patches.
The capability, called Claude Code Security, is currently available in a limited research preview to Enterprise and Team customers.
“It scans codebases for security vulnerabilities and suggests targeted software patches for human review, allowing teams to find and fix security issues that traditional methods often miss,” the company said in a Friday announcement.
Anthropic said the feature aims to leverage AI as a tool to help find and resolve vulnerabilities to counter attacks where threat actors weaponize the same tools to automate vulnerability discovery.
With AI agents increasingly capable of detecting security vulnerabilities that have otherwise escaped human notice, the tech upstart said the same capabilities could be used by adversaries to uncover exploitable weaknesses more quickly than before. Claude Code Security, it added, is designed to counter this kind of AI-enabled attack by giving defenders an advantage and improving the security baseline.
Anthropic claimed that Claude Code Security goes beyond static analysis and scanning for known patterns by reasoning the codebase like a human security researcher, as well as understanding how various components interact, tracing data flows throughout the application, and flagging vulnerabilities that may be missed by rule-based tools.
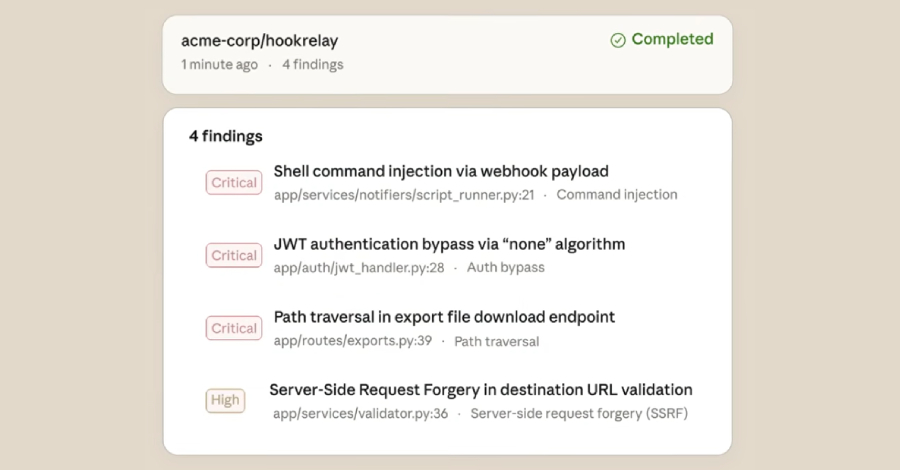
Each of the identified vulnerabilities is then subjected to what it says is a “multi-stage verification process” where the results are re-analyzed to filter out false positives. The vulnerabilities are also assigned a severity rating to help teams focus on the most important ones.
The final results are displayed to the analyst in the Claude Code Security dashboard, where teams can review the code and the suggested patches and approve them. Anthropic also emphasized that the system’s decision-making is driven by a human-in-the-loop (HITL) approach.
“Because these issues often involve nuances that are difficult to assess from source code alone, Claude also provides a confidence rating for each finding,” Anthropic said. “Nothing is applied without human approval: Claude Code Security identifies problems and suggests solutions, but developers always make the call.”