Cybersecurity researchers have discovered two Android spyware campaigns dubbed ProSpy and ToSpy that impersonate apps like Signal and ToTok to target users in the United Arab Emirates (U.A.E.).
Slovak cybersecurity company ESET said the malicious apps are distributed via fake websites and social engineering to trick unsuspecting users into downloading them. Once installed, both the spyware malware strains establish persistent access to compromised Android devices and exfiltrate data.
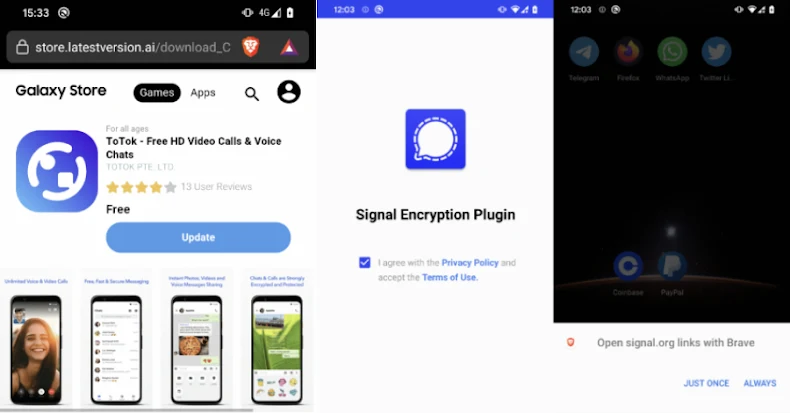
“Neither app containing the spyware was available in official app stores; both required manual installation from third-party websites posing as legitimate services,” ESET researcher Lukáš Štefanko said. Notably, one of the websites distributing the ToSpy malware family mimicked the Samsung Galaxy Store, luring users into manually downloading and installing a malicious version of the ToTok app.”
The ProSpy campaign, discovered in June 2025, is believed to have been ongoing since 2024, leveraging deceptive websites masquerading as Signal and ToTok to host booby-trapped APK files that claim to be upgrades to the respective apps, namely Signal Encryption Plugin and ToTok Pro.
The use of ToTok as a lure is no coincidence, as the app was removed from Google Play and Apple App Store in December 2019 due to concerns that it acted as a spying tool for the U.A.E. government, harvesting users’ conversations, locations, and other data.
The developers of ToTok subsequently went on to claim the removal was an “attack perpetrated against our company by those who hold a dominant position in this market” and that the app does not spy on users.
The rogue ProSpy apps are designed to request permissions to access contacts, SMS messages, and files stored on the device. It’s also capable of exfiltrating device information.
ESET said its telemetry also flagged another Android spyware family actively distributed in the wild and targeting users in the same region around the same time ProSpy was detected. The ToSpy campaign, which likely began on June 30, 2022, and is currently ongoing, has leveraged fake sites impersonating the ToTok app to deliver the malware.
The regionally focused campaigns center around stealing sensitive data files, media, contacts, and chat backups, with the ToTok Pro app propagated in the ProSpy cluster featuring a “CONTINUE” button that, when tapped, redirects the user to the official download page in the web browser and instructs them to download the actual app.
“This redirection is designed to reinforce the illusion of legitimacy,” ESET said. “Any future launches of the malicious ToTok Pro app will instead open the real ToTok app, effectively masking the spyware’s presence. However, the user will still see two apps installed on the device (ToTok and ToTok Pro), which could be suspicious.”
The Signal Encryption Plugin, in a similar manner, includes an “ENABLE” button to deceive the users into downloading the legitimate encrypted messaging app by visiting the signal[.]org site. But unlike the case of ToTok Pro, the rogue Signal app icon is changed to impersonate Google Play Services once the victim grants it all the necessary permissions.
Regardless of the app installed, the spyware embedded within it stealthily exfiltrates the data before the user clicks CONTINUE or ENABLE. This includes device information, SMS messages, contact lists, files, and a list of installed applications.
“Similarly to ProSpy, ToSpy also includes steps designed to further deceive the victim into believing that the malware they just installed is a legitimate app,” Štefanko said. “After the user launches the malicious ToTok app, there are two possible scenarios: either the official ToTok app is installed on the device or it’s not.”
“If the official ToTok app is not installed on the device, ToSpy attempts to redirect the user to the Huawei AppGallery, either through an already installed Huawei app or via the default browser, suggesting the user download the official ToTok app.”
In the event the app is already installed on the device, it displays a fake screen to give the impression that it’s checking for app updates before seamlessly launching the official ToTok app. However, in the background, it collects user contacts, files matching certain extensions, device information, and ToTok data backups (*.ttkmbackup).
To achieve persistence, both the spyware families run a foreground service that displays a persistent notification, use Android’s AlarmManager to repeatedly restart the foreground service if it gets terminated, and automatically launch the necessary background services upon a device reboot.
ESET said the campaigns are being tracked differently due to differences in delivery methods and infrastructure, despite several commonalities in the malware deployed. It’s currently not known who is behind the activity. Nor is there information on either how many or who specifically was targeted by these campaigns, it told The Hacker News.
“Users should remain vigilant when downloading apps from unofficial sources and avoid enabling installation from unknown origins, as well as when installing apps or add-ons outside of official app stores, especially those claiming to enhance trusted services,” the company added.
Update
Google shared the below statement with The Hacker News following the publication of the story –
Android users are automatically protected against known versions of this malware by Google Play Protect, which is on by default on Android devices with Google Play Services. Google Play Protect can warn users or block apps known to exhibit malicious behavior, even when those apps come from sources outside of Play.
(The story was updated after publication to include a response from Google.)