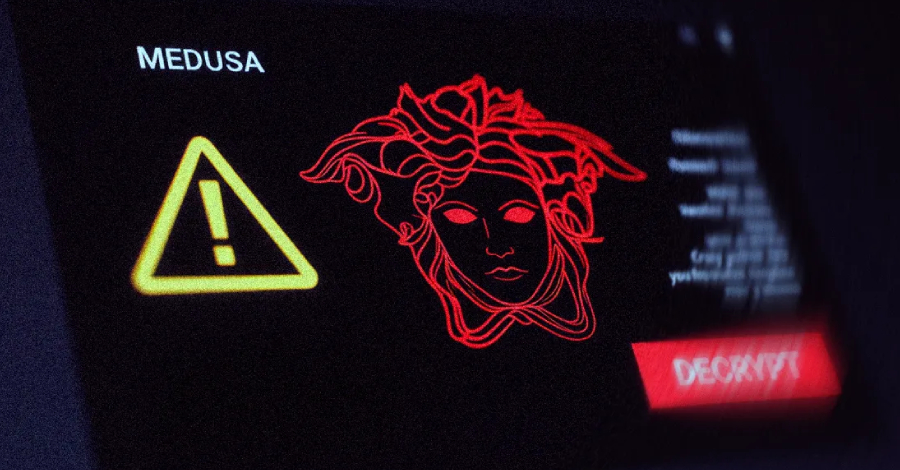
A China-based threat actor known for deploying Medusa ransomware has been linked to the weaponization of a combination of zero-day and N-day vulnerabilities to orchestrate “high-velocity” attacks and break into susceptible internet-facing systems.
“The threat actor’s high operational tempo and proficiency in identifying exposed perimeter assets have proven successful, with recent
Source
Subscribe to Updates
Get the latest creative news from FooBar about art, design and business.
Previous ArticleResearchers Spot Surge in Brute-Force Attacks from Middle East
Related Posts
Add A Comment