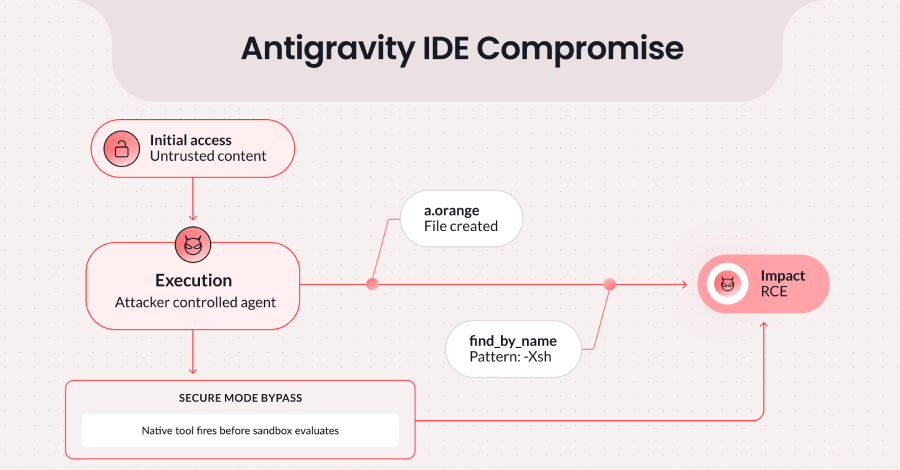
Cybersecurity researchers have discovered a vulnerability in Google’s agentic integrated development environment (IDE), Antigravity, that could be exploited to achieve code execution.
The flaw, since patched, combines Antigravity’s permitted file-creation capabilities with an insufficient input sanitization in Antigravity’s native file-searching tool, find_by_name, to bypass the program’s Strict
Source
Subscribe to Updates
Get the latest creative news from FooBar about art, design and business.
Previous ArticleChinese National Extradited Over Silk Typhoon Cyber Campaign
Related Posts
Add A Comment