Google on Tuesday announced that its new Google Pixel 10 phones support the Coalition for Content Provenance and Authenticity (C2PA) standard out of the box to verify the origin and history of digital content.
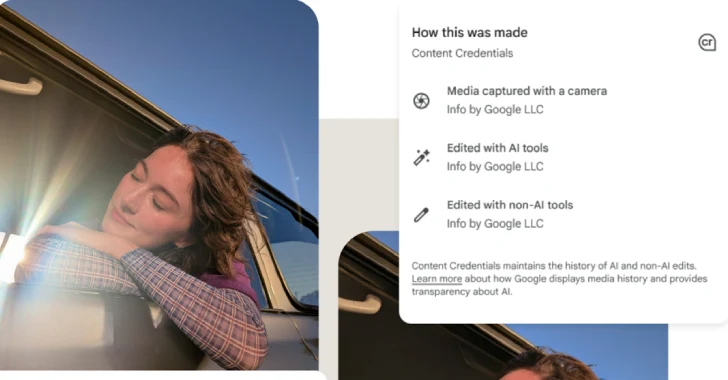
To that end, support for C2PA’s Content Credentials has been added to Pixel Camera and Google Photos apps for Android. The move, Google said, is designed to further digital media transparency.
C2PA’s Content Credentials are a tamper-evident, cryptographically signed digital manifest providing verifiable provenance for digital content such as images, videos, or audio files. The metadata type, according to Adobe, serves as a “digital nutrition label,” giving information about the creator, how it was made, and if it was generated using artificial intelligence (AI).
“The Pixel Camera app achieved Assurance Level 2, the highest security rating currently defined by the C2PA Conformance Program,” Google’s Android Security and C2PA Core teams said. “Assurance Level 2 for a mobile app is currently only possible on the Android platform.”
“Pixel 10 phones support on-device trusted time-stamps, which ensures images captured with your native camera app can be trusted after the certificate expires, even if they were captured when your device was offline.”
The capability is made possible using a combination of Google Tensor G5, Titan M2 security chip, and hardware-backed security features built into the Android operating system.
Google said it has implemented C2PA to be secure, verifiable, and usable offline, thereby ensuring that provenance data is trustworthy, the process is not personally identifiable, and works even when the device is not connected to the internet.
This is achieved using –
- Android Key Attestation to allow Google C2PA Certification Authorities (CAs) to verify that they are communicating with a genuine physical device
- Hardware-backed Android Key Attestation certificates that include the package name and signing certificates associated with the app that requested the generation of the C2PA signing key to verify the request originated from a trusted, registered app
- Generating and storing C2PA claim signing keys using Android StrongBox in the Titan M2 security chip for tamper-resistance
- Anonymous, hardware-backed attestation to certify new cryptographic keys generated on-device without knowing who is using it
- Unique certificates to sign each image, making it “cryptographically impossible” to deanonymize the creator
- On-device, offline Time-Stamping Authority (TSA) component within the Tensor chip to generate cryptographically-signed time-stamps when the camera’s shutter is pressed
“C2PA Content Credentials are not the sole solution for identifying the provenance of digital media,” Google said. “They are, however, a tangible step toward more media transparency and trust as we continue to unlock more human creativity with AI.”