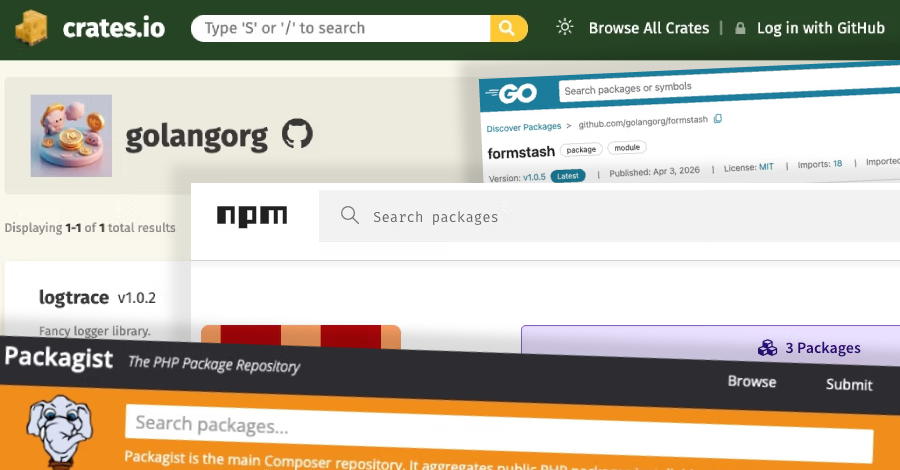
The North Korea-linked persistent campaign known as Contagious Interview has spread its tentacles by publishing malicious packages targeting the Go, Rust, and PHP ecosystems.
“The threat actor’s packages were designed to impersonate legitimate developer tooling […], while quietly functioning as malware loaders, extending Contagious Interview’s established playbook into a coordinated
Source
Subscribe to Updates
Get the latest creative news from FooBar about art, design and business.
Related Posts
Add A Comment