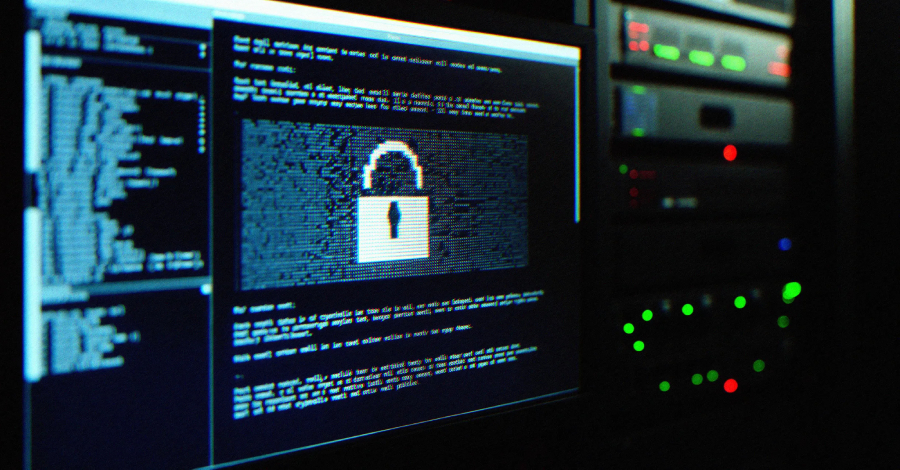
Threat actors associated with Qilin and Warlock ransomware operations have been observed using the bring your own vulnerable driver (BYOVD) technique to silence security tools running on compromised hosts, according to findings from Cisco Talos and Trend Micro.
Qilin attacks analyzed by Talos have been found to deploy a malicious DLL named “msimg32.dll,”
Source
Subscribe to Updates
Get the latest creative news from FooBar about art, design and business.
Previous ArticleMirax Android Trojan Turns Devices Into Residential Proxy Nodes
Next Article Operation Atlantic Seizes $12m in Crypto Losses
Related Posts
Add A Comment