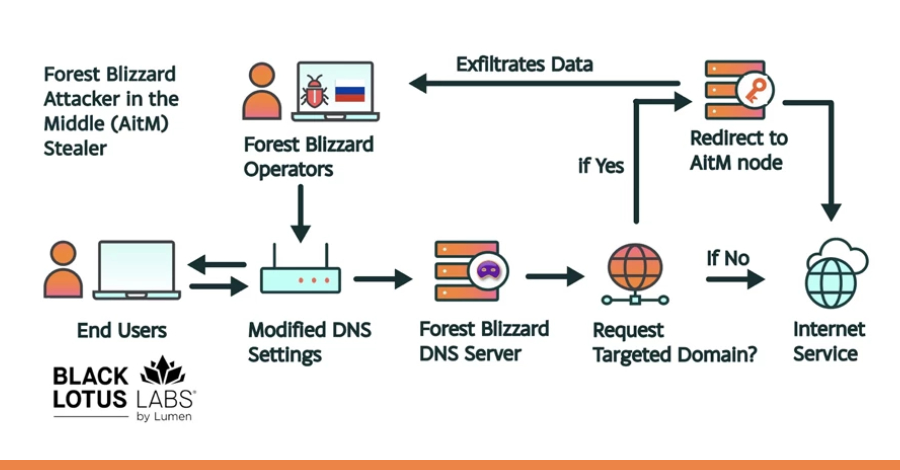
The Russia-linked threat actor known as APT28 (aka Forest Blizzard) has been linked to a new campaign that has compromised insecure MikroTik and TP-Link routers and modified their settings to turn them into malicious infrastructure under their control as part of a cyber espionage campaign since at least May 2025.
The large-scale exploitation campaign has been codenamed
Source
Subscribe to Updates
Get the latest creative news from FooBar about art, design and business.
Previous ArticleNIST Drops NVD Enrichment for Pre-March 2026 Vulnerabilities
Related Posts
Add A Comment