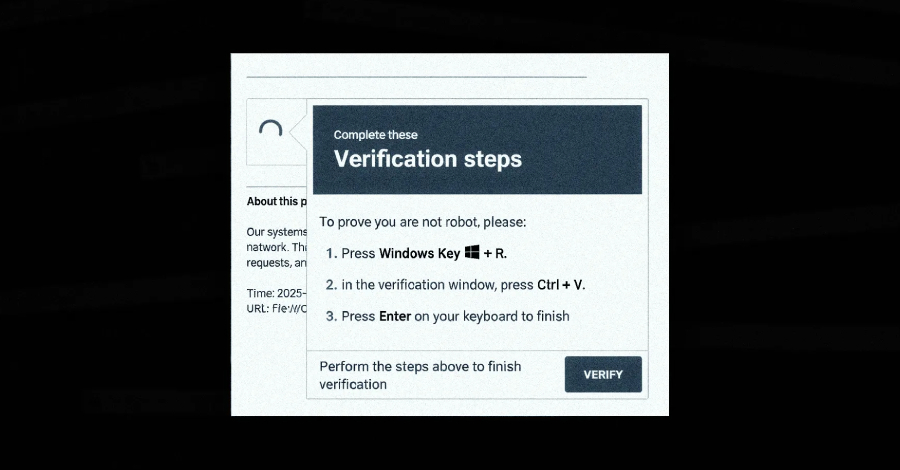
A new campaign has leveraged the ClickFix social engineering tactic as a way to distribute a previously undocumented malware loader referred to as DeepLoad.
“It likely uses AI-assisted obfuscation and process injection to evade static scanning, while credential theft starts immediately and captures passwords and sessions even if the primary loader is blocked,” ReliaQuest researchers Thassanai
Source
Subscribe to Updates
Get the latest creative news from FooBar about art, design and business.
Previous ArticleWhen the World Splits: Are Businesses Really Ready?
Next Article GPU Rowhammer Attack Enables Privilege Escalation
Related Posts
Add A Comment