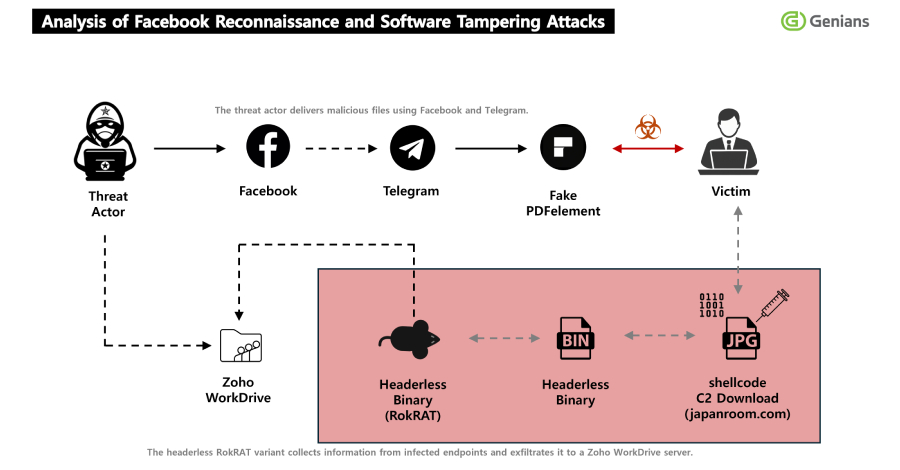
The North Korean hacking group tracked as APT37 (aka ScarCruft) has been attributed to a fresh multi-stage, social engineering campaign in which threat actors approached targets on Facebook and added them as friends on the social media platform, turning the trust-building exercise into a delivery channel for a remote access trojan called RokRAT.
“The threat actor used two Facebook
Source
Subscribe to Updates
Get the latest creative news from FooBar about art, design and business.
Previous ArticleCrypto Exchange Grinex Blames Western Spies for $13m Theft
Related Posts
Add A Comment